Start your unattended server wherever you are in the world over the internet. A complete tutorial on wake-on-LAN (WOL) with a reverse SSH tunnel using nothing more than a Raspberry Pi.
Today, we continue our series on readying the homelab for unattended access. Previously, we set up a Raspberry Pi to allow us to remote into our network via a reverse SSH tunnel. That's useful by itself, especially as a backup if our normal route of access (VPN) is down, but we can also use that same reverse SSH tunnel to do some other incredibly useful things such as waking up other devices on the network with wake-on-LAN (WOL). Today's tutorial will focus on precisely that: enabling our servers to be woken up on LAN, and configuring our RPi sleeper cell to wake those servers up. Let's begin!
Enable Server for Wake-On-LAN (WOL):
1. On your server, install ethtool:
sudo apt install ethtoolethtool allows us to verify that our NIC can support wake-on-lan. It is also used to enable wake-on-LAN on Ubuntu.
2. Find the name of the network adapter you are currently using with the following command:
ifconfigIf you don't already have ifconfig, you can install it with:
sudo apt install net-toolsIf you need help figuring out which network adapter you are currently using, look for the one with an IP address assigned. You can also look at which network adapter has had traffic go through it (the RX and TX packets line will have non-blank values):
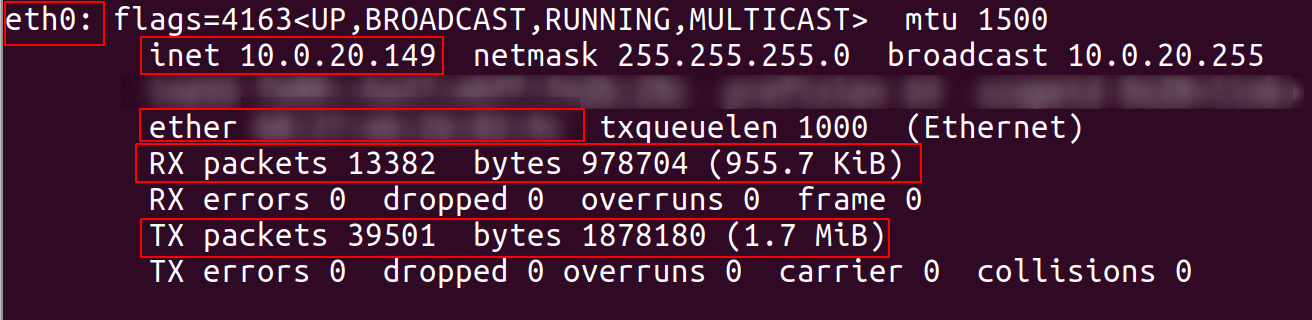
In my case, eth0 is the network adapter in use, and chances are it probably is for you too. If you need help with this, feel free to ask me in the comments/forum.
3. While you're here, record the address next to ether (highlighted above). That's your MAC address and that's how we will ultimately address the server when we are ready to wake it up.
4. Check to see if wake-on-LAN is available on your NIC with ethtool:
sudo ethtool <adapter name from above>In my case that command would be:
sudo ethtool eth0If WOL is available on your card, you should see a line that appears as so:
Supports Wake-on: pumbgWe really only care to see that this line contains a "g", indicating a that it will accept a "magic packet" (the mechanism by which wake-on-LAN works).
N.B.: If you don't see it, all hope is not lost, you may just need to enable "Wake-On-LAN" in the BIOS. This varies from motherboard to motherboard but almost all have this setting so look for it.
5. Enable the system for Wake-On-LAN:
sudo ethtool -s eth0 wol gDon't forget to replace eth0 with the adapter you're using if you have a different one.
6. Create the script to insure that WOL is always enabled:
Now, there's an unpleasant little "feature" in OS's where the above setting gets reset after every reboot.
If you're using unRAID, this easily handled with the User Scripts plugin. Just create a user script with the following content and set it to run "At startup of array" (make sure you have the array set to always start):
#!/bin/bash
ethtool -s eth0 wol gIf you're using Ubuntu, we'll need to create a system service:
sudo nano /etc/systemd/system/wakeOnLAN.serviceIn this add the following:
[Unit]
Description=Re-enable WOL
[Service]
Type=oneshot
ExecStart=/sbin/ethtool -s eth0 wol g
[Install]
WantedBy=basic.targetAgain, don't forget to replace eth0 with whatever network adapter you're using.
Enable the service:
sudo systemctl enable wakeOnLAN.serviceThat's it for setting everything up on the server side. Now, let's set everything up on our RPi (or whatever other device you have the reverse SSH tunnel set up on).
Install Etherwake on RPi:
7. Super easy job here. Just install etherwake on the RPi with:
sudo apt install etherwakeThat's all!
Test Everything Out:
8. Shutdown your server so we can test waking it up.
9. SSH (reverse SSH if working remotely) into your RPi.
10. Just like we did in Step 2 above, identify the network device in use on your RPi.
This is where A LOT of people trip up and why they fail to get wake-on-LAN/etherwake working. By default, etherwake attempts to send out the WOL magic packet on eth0 of the device it's being run on. If eth0 isn't in use, you'll get the following error message:
SIOCGIFHWADDR on eth0 failed: No such device11. Send the WOL magic packet with the following command using the MAC address you found in Step 2/3 above and the RPi network device you found in step 10 above:
sudo etherwake <MAC Address of Server Network Device Here> -i <RPi Network Device from Above> Example:
sudo etherwake ab:cd:ef:gk:hi:jk -i eth0At this point, you should hear your server kick on and boot up!
As always, let me know if you run into any problems or have any questions in the comments below!
Interested in this topic and others like it? Join our community and join in the discussion! We currently have a need for moderators so if you can help out it would be much appreciated!