If you’re running a web server out of your homelab (and you should), you really should consider running your servers behind an NGINX reverse proxy. Honestly, this should be the first thing you build in your homelab. It doesn’t take a lot to setup- NGINX is so efficient it can even be run on something as simple as a Raspberry Pi and it pays you back in dividends once you’ve got it up and running.
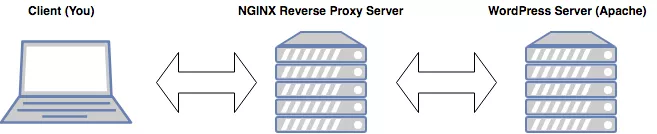
What Does a Reverse Proxy Do?
A reverse proxy serves as a sort of dispatcher by acting as a central contact point for clients. Based on the information requested by the client, it then routes the request to the appropriate backend server and makes sure the backend server’s response makes it back to the appropriate client.
What are these dividends you speak of?
A reverse proxy can give you additional flexibility, security, and even a performance bump. It can also greatly simplify your deployment:
- Flexibility: An NGINX reverse proxy can allow you to host multiple sites/domains with only one IP address. It accomplishes this by listening on a port (usually port 80 for HTTP traffic) and parsing the http request header for the host. Based on the host specified in the header, NGINX can route a request to the proper backend server (in a reverse proxy, this is also known as an upstream server).
- Security: By standing between the client and the backend server, the reverse proxy provides a degree of separation.
- Improved performance: NGINX can be used to cache static content which means that not only is content returned faster to the client, but since it often means that the upstream server doesn’t even need to be contacted, it can take a lot of the load off your backend servers.
- Simplifies your deployment: If you’re hosting multiple sites, an NGINX reverse proxy can greatly simplify your implementation by giving you a single point to manage your traffic. This means you only have to set up port forwarding once and whenever you create a new site, all you have to do is add an additional configuration listing to NGINX. When you implement HTTPS (and you should), instead of having to implement it on every individual web server you have setup, you can handle it all on your NGINX reverse proxy.
Installing NGINX:
Now that I’ve hopefully convinced you to implement an NGINX reverse proxy, let’s get started. I recommend using a dedicated device for this (again, it need not be expensive, even a Raspberry Pi will do) but it helps keep everything clean and compartmentalized. With a clean install of Ubuntu (if using an x86-64/AMD64 device) or Raspbian (if on the RPi), do the following:
1. Update your package list and make sure your device is updated:
sudo apt-get update
sudo apt-get upgrade2. Depending on what Linux distro you’ve picked, it might have Apache already installed. We don’t want that so uninstall it with:
sudo apt-get remove apache23. Install NGINX:
sudo apt-get install nginx4. NGINX should start automatically, but just in case, you can start it manually with:
sudo systemctl start nginx5. Confirm that NGINX is up and running by opening your browser and visiting your IP address. You should be able to get the default page to display by visiting your loopback IP address (127.0.0.1) or the actual IP assigned to your device (available by running the command ‘hostname -I’ in the terminal):
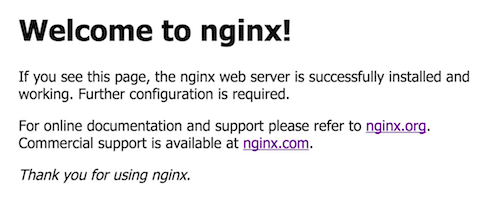
6. Good! Now we have NGINX up and running! If you don’t have a backend web server running yet, then we’re done since you don’t have anywhere for us to send traffic. Come back to this point when you do. But if you do have a web server for us to proxy traffic to/from, continue on!
Configuring the Reverse Proxy:
So you’ve made it this far and you now have an NGINX server running. Let’s set up the reverse proxy part to make this an NGINX reverse proxyand not just a simple NGINX web server:
1. Go to our NGINX sites-available directory:
cd /etc/nginx/sites-available/2. Create the configuration file. You’ll eventually accumulate a lot of these, so I recommend naming it based on the site that you’re reverse proxying so you can easily find it again:
sudo nano example.com.conf3. In nano, add the following:
server {
listen 80;
server_name example.com;
location / {
proxy_pass http://192.x.x.2;
}
}server_name is going to contain the domain name of the website clients are going to be requesting. proxy_pass is going to be the local (internal) IP address of the web server that you’re forwarding traffic to. You can also specify a particular port if your web server is running on a non-standard port (example: proxy_pass http://192.x.x.2:82300).
4. For NGINX to actually serve your site with your new configuration, you need to link it to /sites-enabled/ with:
ln -s /etc/nginx/sites-available/example.com.conf /etc/nginx/sites-enabled/example.com.conf5. Test your configuration to make sure you aren't getting any errors:
sudo nginx -t6. Reload NGINX to tell it that the configuration has been updated:
sudo systemctl reload nginxThat's all there is to it! Once you've completed the steps here, check out the next guide in the series to get your RPi NGINX reverse proxy connected to the internet.
Changelog
Update (11/11/19): The next guide in this series, covering how to connect your new RPi NGINX server to the Internet, has been published due to popular request.
In future posts, I'll cover how to setup that upstream web server, how to configure the DNS for your domain, and port forwarding so that you can access your sites on the internet.
As always, feel free to comment if you run into any problems or need help!
