Secure your network by learning how to set up access control lists (ACLs) on the HP 1910 (Comware) managed switch.
In a previous guide, I discussed implementing VLANs on an HP 1910 L3 managed switch (Comware-based). In today's guide, I will discuss how to secure those VLANs by setting up access control lists (ACLs).
What is an Access Control List (ACL) and why do I need one?
An ACL is like a firewall- it blocks connections based on a set of rules. They are typically used to control traffic flow between VLANs. More typically, they are used to secure VLANs from each other.
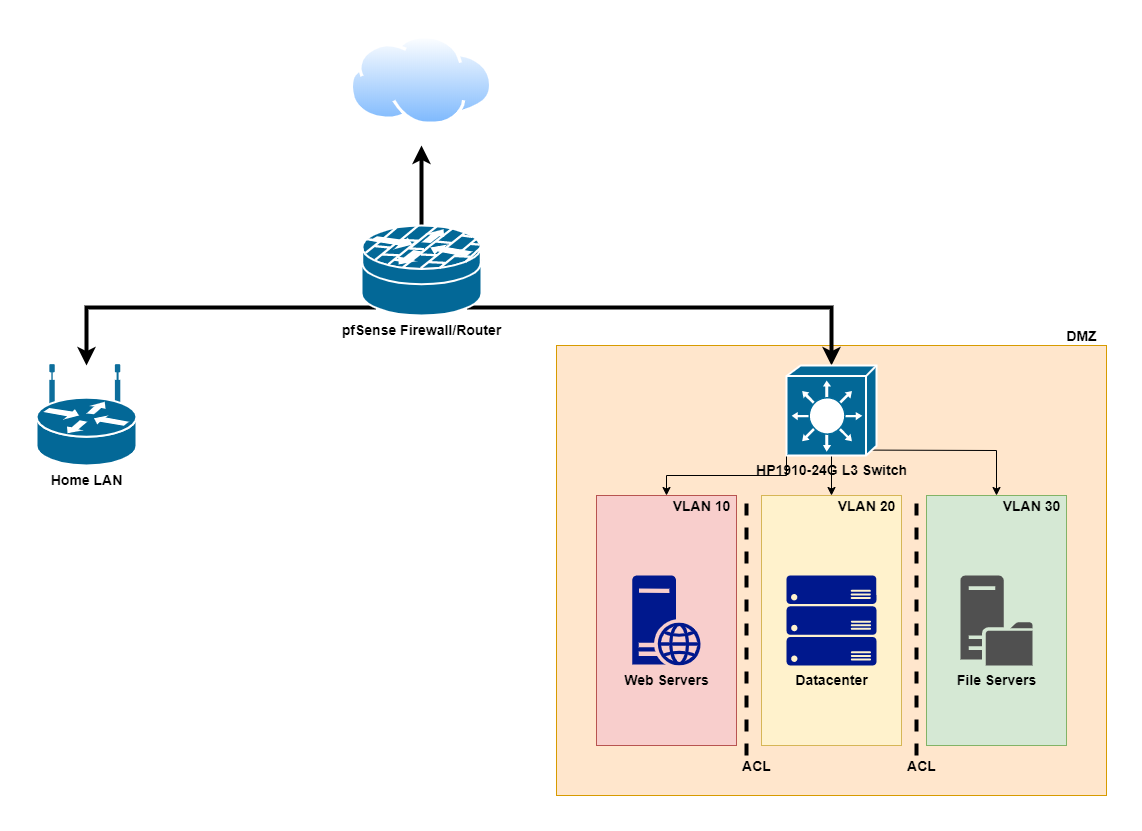
For example, in my homelab, I have a DMZ (demilitarized zone) network which contains all of my servers that are web-facing or even touching a server that is web-facing. This is done so that, in the event of a compromise, the worst-case scenario is that the attackers only have access to those servers and not my home network. As an additional layer of protection, that DMZ is then further subdivided into three separate VLANs: one for my web servers, another for my "data center" (virtualization servers hosting various VMs), and another for storage/backups. Obviously, the web server VLAN is the highest risk since it has the greatest exposure to the internet. In order to compartmentalize that VLAN, I have implemented ACL rules to prohibit it from talking to the other VLANs. Thus the utility of ACLs.
ACLs vs. Firewalls- Stateless vs Stateful Inspection
An ACL is technically different from a firewall in that a firewall does "stateful" inspection of traffic, which is a fancy way of saying that it keeps track of connections. For example, let's say you visit a website on the internet. In doing so, you establish an outbound connection to an outside web server. The web server responds to your request and sends a message back. The firewall knows you sent traffic out to that web server, so it opens the port and allows the server's response to come back to you.
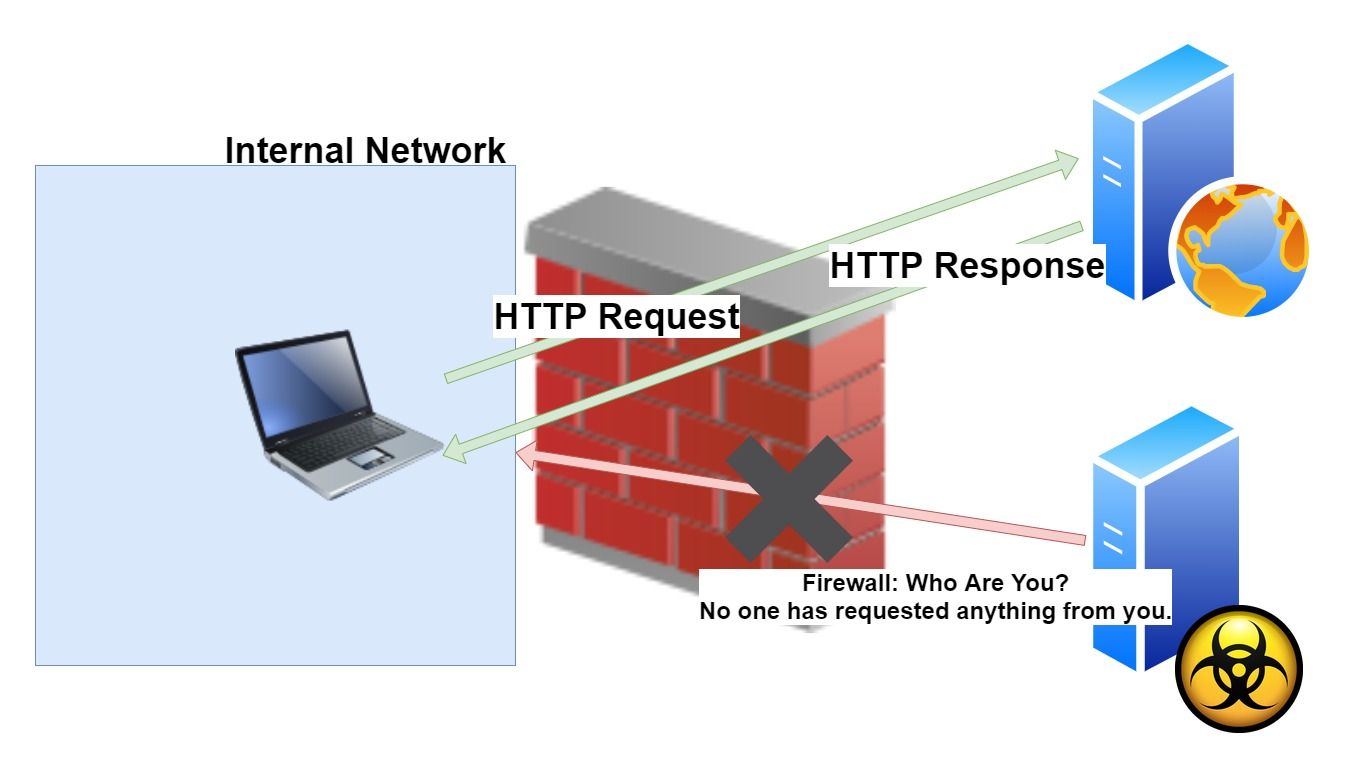
In contrast, an ACL does "stateless" inspection. I.e. it doesn't track connections. It's a brute force set of hard rules that just look for a match of what's written. It doesn't matter that the traffic may have been a response to a request, if that traffic matches a deny rule, it's dropped. End of story.
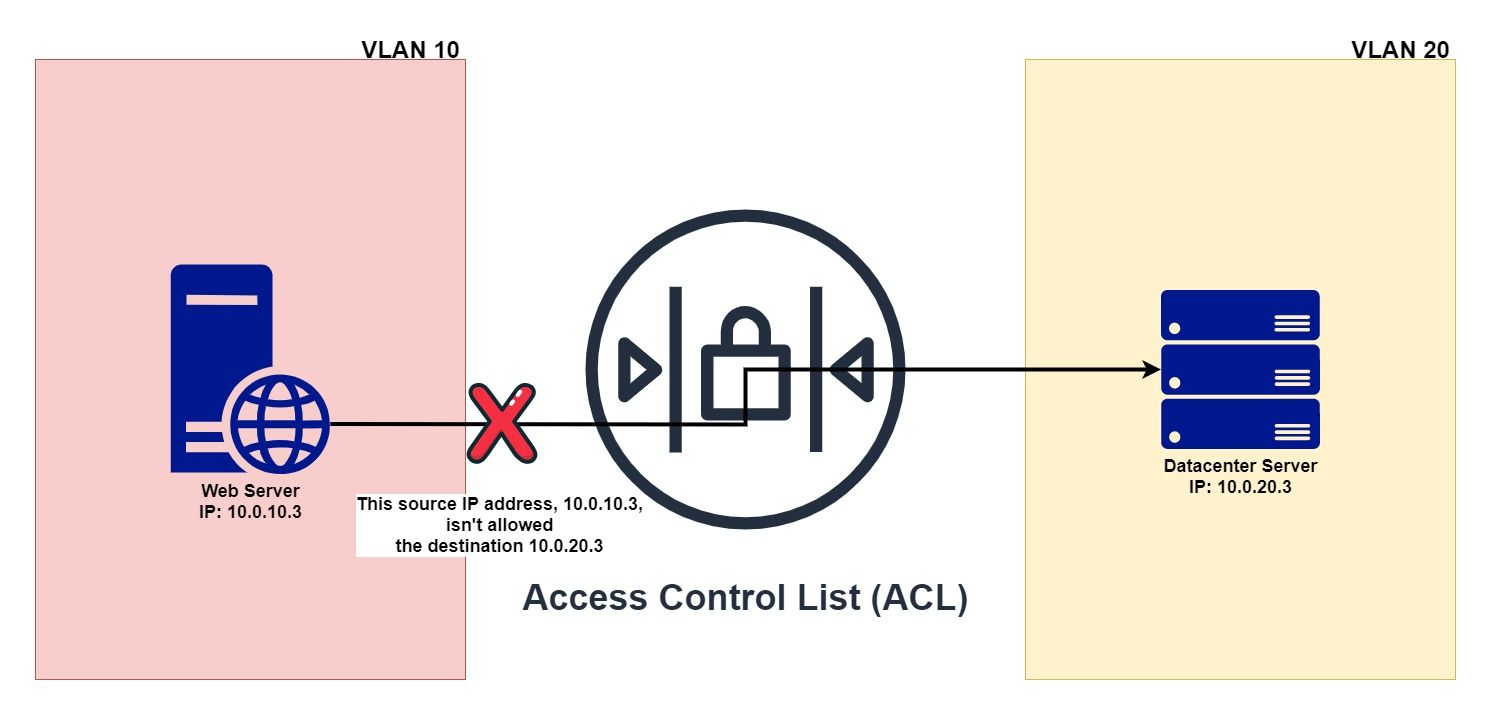
This actually has some advantages though. Chief among them is that because these ACLs consist of hard rules that are just matching on source and destination IP addresses, they can be implemented in hardware. That means they're fast, really fast. On a network that has multiple VLANs on it that may still need to communicate with each other, this means line rate speed stays fast.
Why is this guide needed? Why am I calling it "The Easy Way"?
Overall, I like the switch, but my biggest complaint is the burdensome way in which HP implemented configuring access control lists in their web GUI interface. It is the single-worst ACL implementation I have ever seen.
Normally, when you set up an ACL, all you have to do is:
- Create the ACL.
- Add your rules to the ACL.
- Apply your ACL to the interface.
But does HP do it that way with their front-end? Oh no, instead you have to do all of the following through the GUI:
- Create the ACL.
- Create your rules.
- Create a QoS classifier.
- Apply your ACL to that QoS classifier.
- Create a QoS behavior.
- Create a QoS policy.
- Link that QoS classifier to the behavior with the policy.
- Apply that policy to an interface.
Oh, and by the way, that interface has to be one of the switch ports. You can't apply it to an entire VLAN interface, which means you then have to apply that policy to every single port you use. It's a complete maintenance nightmare. My blood pressure rises just thinking about it.
It's so bad that there have been several times I considered just abandoning my HP switch, writing it off as a sunk cost/learning experience, and moving onto a Cisco switch (or just implementing a router-on-a-stick).
But don't despair! I have developed a way that will allow you to implement ACLs the "normal way" described above on an HP 1910 (and other Comware-based) switches. It even allows us to apply the ACL to the VLAN interface, saving us a lot of work and maintenance headaches! Let's begin!
How to Set Up ACLs On The HP 1910 Switch
We're going to try and take the best of both worlds here- using the GUI to make the ACL + rules and the command line to apply them to an interface.
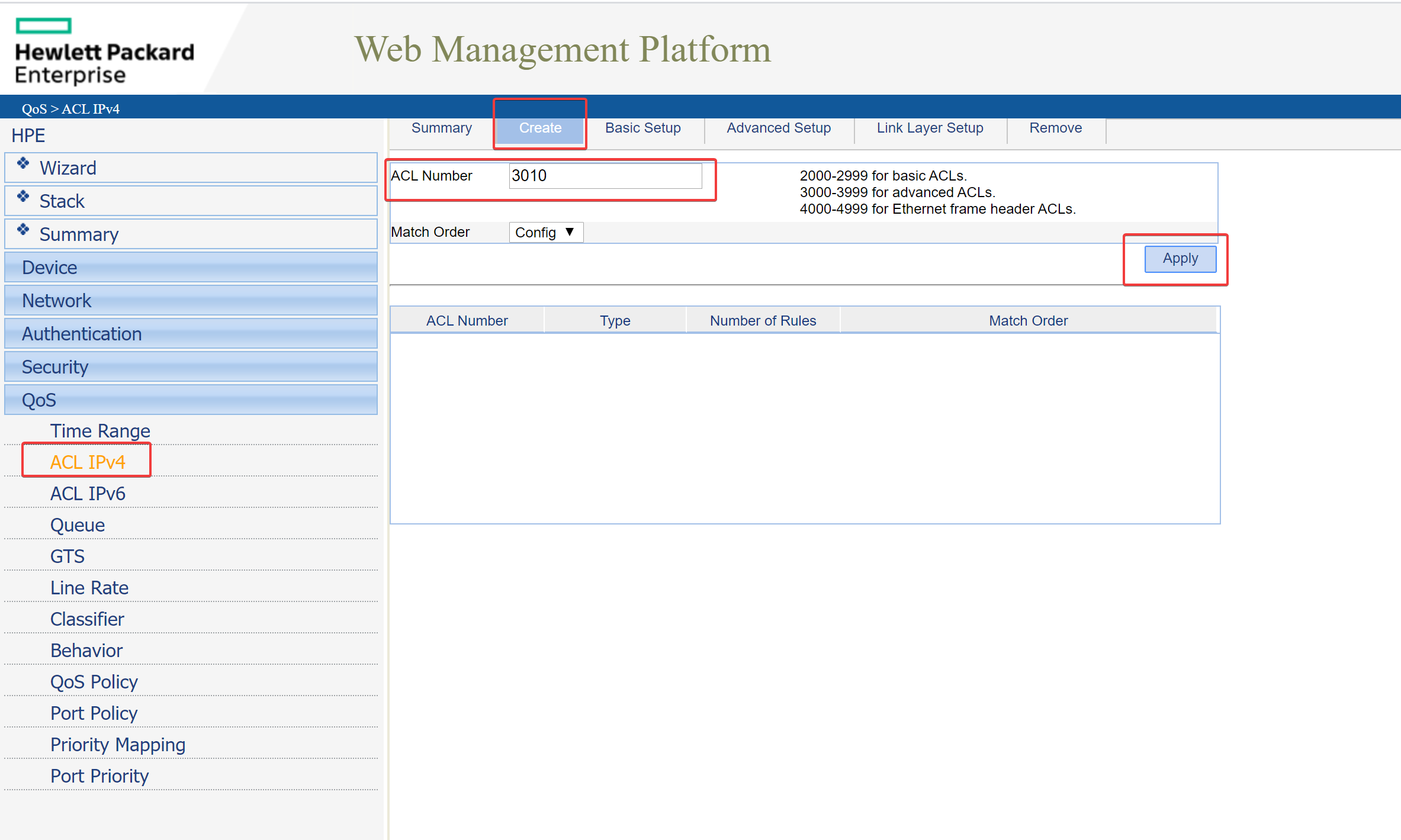
Create the ACL:
1. On the switch's web GUI, navigate to QoS > ACL IPv4. Enter a number for your ACL and click apply:
Add Rules to ACL:
2. In the same ACL IPv4 section, navigate to the "Advanced Setup" area and set up your rule:
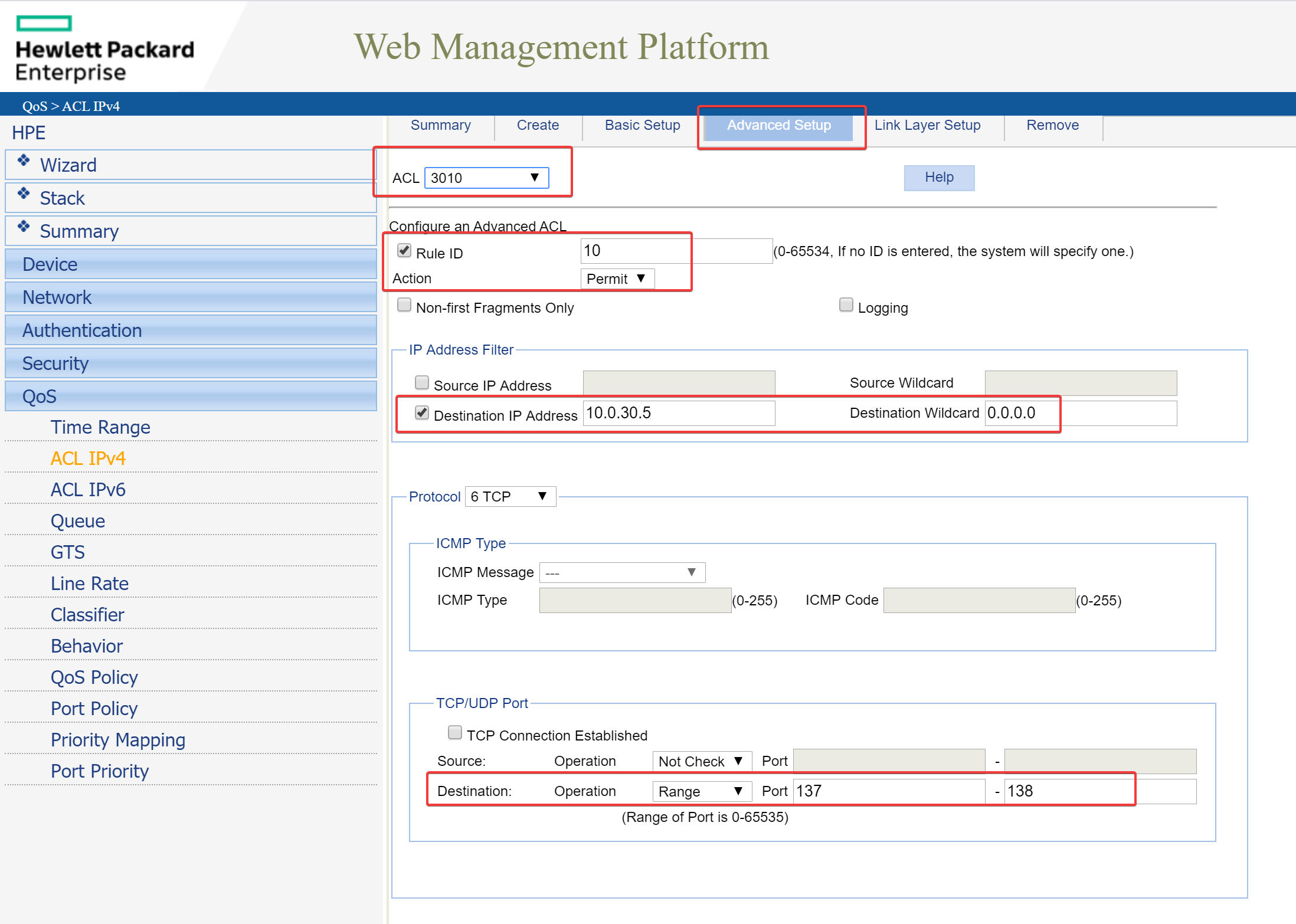
Hopefully you understand that what rules you actually need to create is dependent on your specific usage and as such is outside of the scope of this article. However, if you would like to consult with me, feel free to ask in the comments below or in the forum. I won't even charge you! 😉
Apply ACL to Interface
Once you've added all the rules you need to the ACL, we'll now need to use the command line. SSH into your switch.
3. Once you're SSH'd in, we're going to use the "advanced CLI" of the HP switch, which lets us use actual Comware commands. To do so, enter the following:
_cmdline-mode onYou'll then be prompted for a password which is either:
512900or
Jinhua1920unauthorized4. Go to the system-view:
system-view5. Navigate to the appropriate interface. In my case, since I am going to apply the ACL to my VLAN interface, I use the following command:
interface Vlan-interface <ENTER VLAN NUMBER HERE>Note that you can also apply an ACL to the gigabit ethernet interfaces. If you don't know what interfaces are available, download your current configuration (Device > Configuration > Backup) and open it up in a text editor:
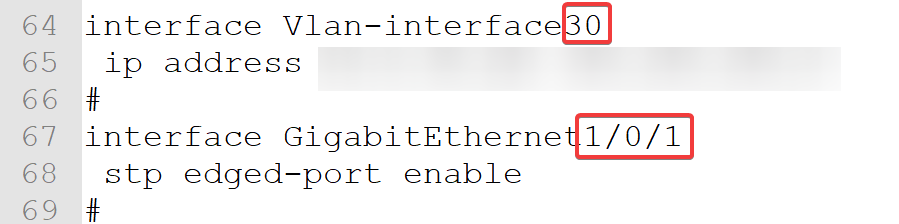
So, for the example above, if you wanted to apply the ACL to the VLAN interface, you would use the following command:
interface Vlan-interface 30If you wanted to apply the ACL to an individual gigabit ethernet interface (i.e. a port):
interface GigabitEthernet 1/0/16. Apply the ACL you created in step 1 to the interface:
packet-filter <ACL number here> inboundIn my case, my ACL is 3010 so:
packet-filter 3010 inbound7. Save to apply:
saveYou can now run your tests to verify that your ACL works (i.e. pinging from devices within the VLAN).
Other Useful Commands:
Remove an Applied ACL:
Don't worry if you mess things up, you can undo what you've done by navigating back to the interface as you did above and running the command:
undo packet-filter <ACL number here> inbound
save